EMPLOYEE SURVEYS
Your finger on the pulse
Employee surveys sent with Relesys make it quick and easy for you to understand your frontline workforce. With advanced surveying tools and rich data reporting, you and your team get fast access to the insights you need to deliver a world-class employee experience.

The better way to survey the frontline
Insights powered by AI
for a 360 view of employee satisfaction for HQ and Managers
Sky-high response rates
from surveys sent to your employees in the Relesys app
Time back to take action
previously spent building, sending, and analyzing results
How it works

Build
Rapidly create surveys in a friendly interface within your admin panel.
Easily configure the format with familiar single and multi-question formats, 5-point scales and free-text fields.
Prepare questions to spot trends by tagging them with 'engagement drivers’.

Send
Target specific audiences to ensure the right questions reach the right teams.
Personalize the experience with auto-translation and employee 'complete later' options.
Ensure sky-high completion rates thanks to in-app nudges, points awarded via gamification, and anonymous responses.

Learn
Get the full picture through rich data visualizations of user feedback, including AI-prioritized sentiment analysis.
Slice responses to spot trends by region, department, role and more. Or export raw data to analyze in BI tools.
Empower local managers to take action with survey respondent reporting for them in-app.

Survey PRO
Extend the experience with...
Tracking surveys
Send surveys at regular intervals to track changes in employee engagement levels and identify areas of strength or areas needing attention.
Frontline insights
Empower HQ and local managers with rich data reporting to spot changes, trends, or patterns in employee perceptions and experiences.

See other solutions
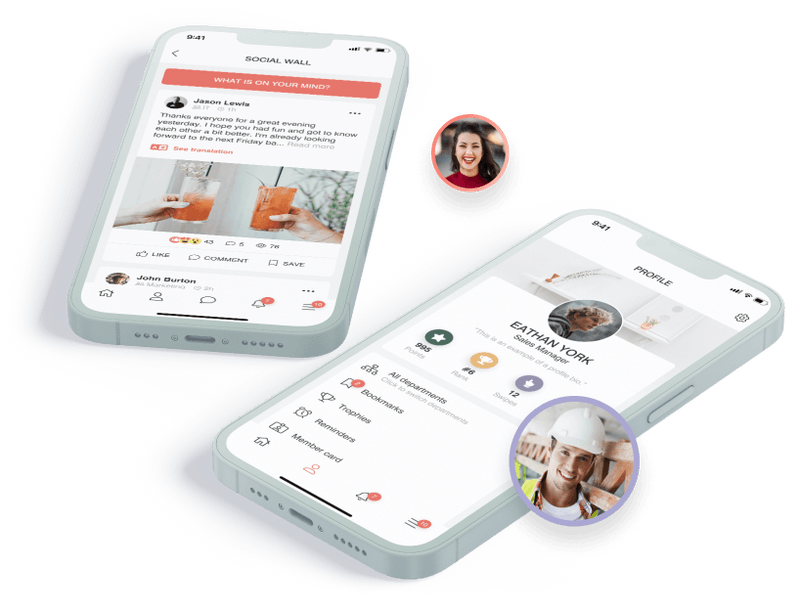
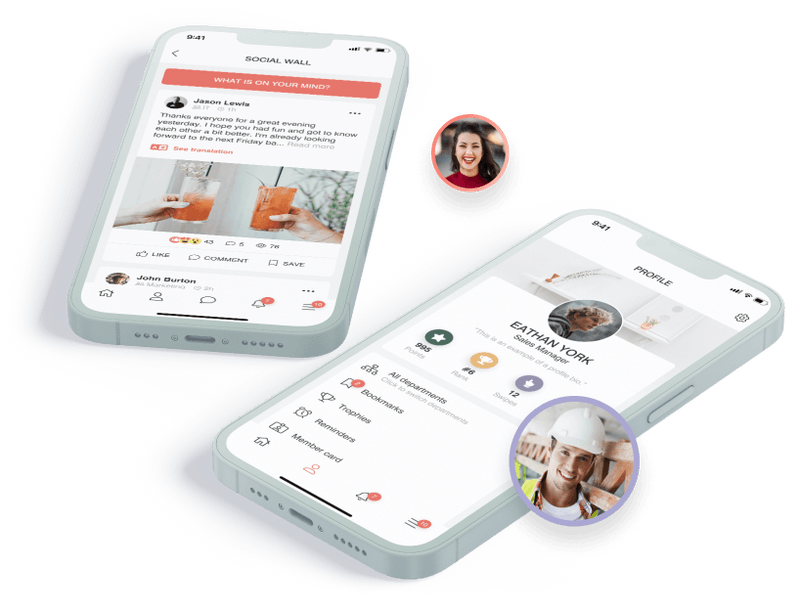
Engage your workforce with the Relesys app

